Should Att Smart Wifi Have Draw Over Other Apps And Modifie System Permission On My Phone?
Nosotros are reader supported and may receive a commission when you make purchases using the links on our site.
How to secure your Android app permissions
@VPN_News UPDATED: August 26, 2021

How often practise you become a question on your Android device about whether yous desire to give an app access to some application or other? This piddling popup appears and so often that many people click on "Allow" without giving it a 2nd thought.
Do y'all know how many apps you have given admission to your personal information? While you hope that app-owners won't corruption this access, with accusations rife against information-hungry companies similar Facebook, you tin't be too careful.
Thankfully, with a little know-how, you lot can take steps to secure your Android device past changing your settings manually. In this post, nosotros explain how to do just that.
How to discover app permissions
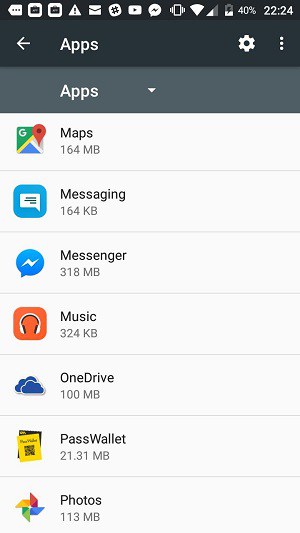
Data on the permissions that your apps have is easy to get together. First, go to the Settings screen. Curl downwardly to the Device section and and then tap on Apps.

The next screen lists all of the apps on your phone.
Tap on an app to run into all options. Select Permissions.
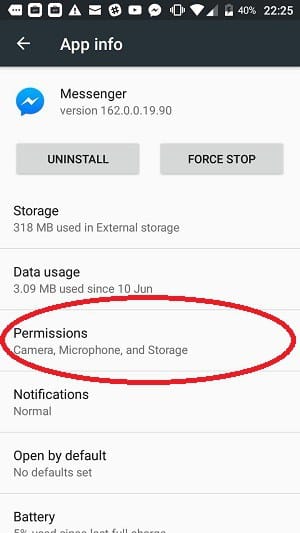
Now y'all can see the permissions that you granted to the selected apps.
Withdrawing permissions from apps
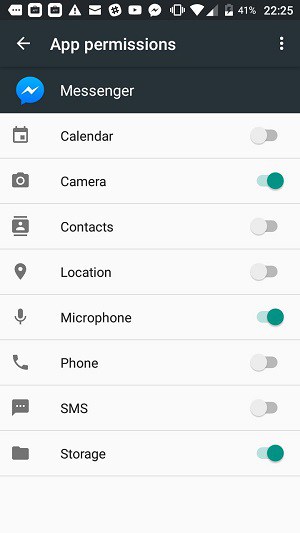
The services on your phone that apps can gain permission to admission are:
- Calendar
- Camera
- Contacts
- Location
- Microphone
- Telephone
- SMS
- Storage
If y'all granted access to one of these data stores or services, you can accept that permission abroad past tapping on the slider next to the permission category.
Permission categories
Each of those categories you see in the permission screen for each app is not the proper noun of an app, but the proper name of a category of apps. The Android operating organisation includes access functions that enable independently-written utilities to access the services of the operating system. There are a number of functions that each of these categories in the Permissions screen requite admission to.
Giving permission to access i of these categories gives apps access to operating system functions. Android contains all apps in a "sandbox", which is an isolated environment that keeps those apps away from the operating system. Permissions break through that security mensurate.
Configure app permissions
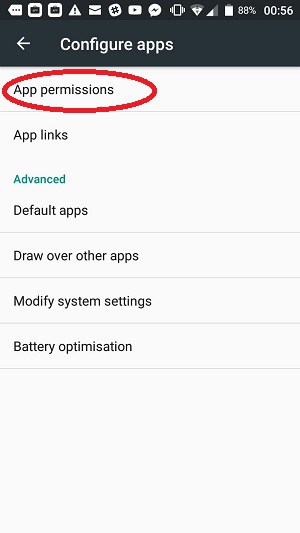
Y'all can go another view of your app permissions through the Configure apps menu. To navigate to this location, go back to the Settings screen, tap on Apps, and and so press the cog symbol in the header of the Apps screen.
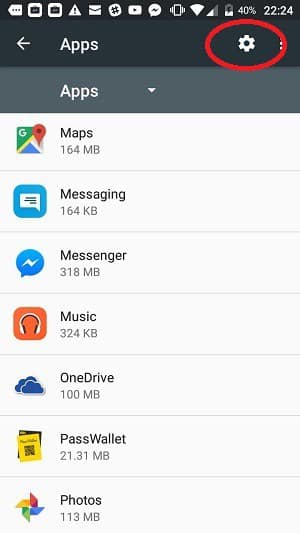
This gives you the Configure apps options. Tap on App permissions to go on.
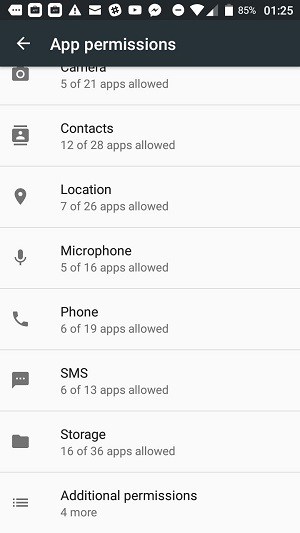
In the App permissions screen, y'all will meet an option that wasn't available in the list of permissions categories that you arrived at by examining individual apps. This is the Torso sensors category.
A line below each category tells you how many apps have that permission and how many apps installed on your phone could feasibly use that permission. This bulletin is the format X of Y apps allowed where 10 is the number of apps with access and Y is the number of the apps with capabilities to use that category of service.
Click on i of these categories to become a list of all apps that have that permission.
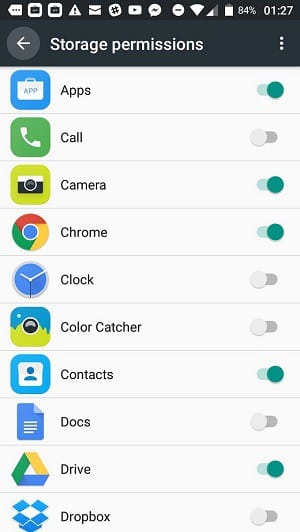
Click on the slider adjacent to a category to turn its accessibility off. All apps that accept this permission will have that admission removed.
Back in the Configure apps screen, gyre down to the bottom of the permissions listing. Yous volition see that the last listing item is called Additional permissions.
In the Additional permissions screen you lot volition come across four options:
- Car information
- Read email attachments
- Read instant messages
- Write instant messages
If yous tap on an option that lists the number of apps that apply to that category as 0 of 0, the resulting screen will simply read No permissions. If any of those categories could be used by at least one app on your phone, borer on that category would lead to an app list that gives y'all the choice of turning each use off with a slider.
Deny app admission to arrangement settings
Although this guide is focused on "app permissions," the chore of securing your phone would non be complete without checking on the organization settings that apps are allowed access to. You can view these settings via the Configure apps screen.
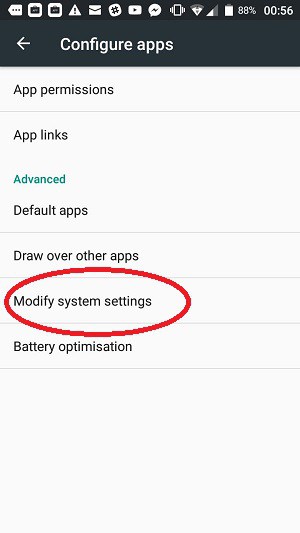
Tap on Modify system settings to proceed. The next screen shows every app installed on your telephone with a message that tells you whether it can modify arrangement settings.
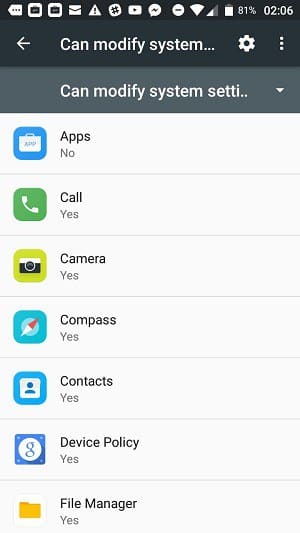
Tap on ane of these apps to encounter a slider that enables you to block the app from accessing system settings.
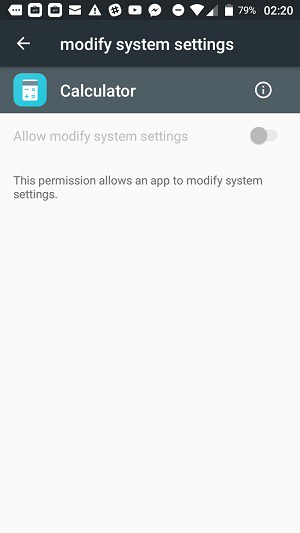
The idea of letting apps access your system is worrying. Information technology is difficult to empathize which settings each app needs considering they are itemized on the screens. There is no "Settings" folio that provides details.
Prevent overlays
Malware can masquerade as a genuine app. You might click on Allow to a permissions demand without realizing that the app name that seems genuine is really an illegal app that contains a deceptive function. Such a malicious app can detect the apps that you want to open up then overlay them, mimicking the existent app.
These types of apps are designed to get together authentication credentials for real online services. They can accomplish this goal by making certain that the false app covers the real version that you opened.
In order to perform this play tricks, the malware app needs to reach the status of ever being on top of all open apps. You can turn off this adequacy. Go back to the Configure apps screen.
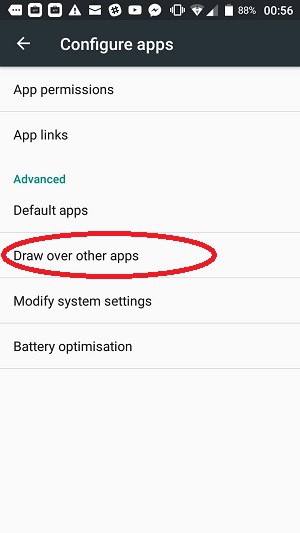
Tap on Depict over other apps to see which apps can overlay the screen. In the following list, you will see each installed app and whether information technology can overlay others.
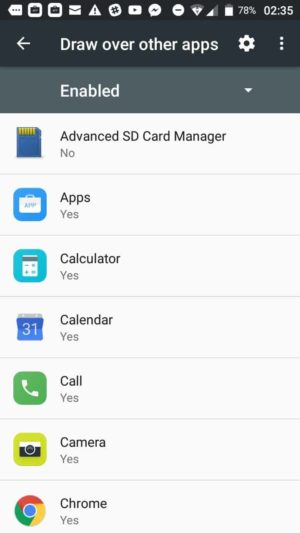
To remove this permission, tap on an app that has the permission that you want to remove. This will take yous to a screen in which you tin plow the permission off with a slider.
App permission consequences
Now let's take a look at some of the categories that apps might enquire for access to. The consequences of granting admission tin can exist very damaging.
SMS permissions
If you allow a new app to access SMS, that new utility will be able to access MMS messaging systems too every bit any SMS app you have on your telephone, not just the one default SMS tool that comes with the Android operating arrangement.
Furthermore, an app with permission to access SMS will be able to read all of the messages you have stored in your SMS apps. Information technology will too exist able to intercept and read (and possibly alter) incoming messages and it will fifty-fifty be immune to send out SMS messages from your telephone.
Telephone call permissions
The permission to access any advice service on your phone is a souvenir to any malware that wants to replicate itself by sending out Trojan programs to your Contacts list. If the worm can send those infections out from your Telephone number, the hacker that wrote the original virus saves a lot of money and as well hides his identity.
A malicious money-making app with permission to access your phone's phone call functions can rack upwardly your bill and brand a ton of money for its possessor by making repeated calls to premium numbers owned by the hacker.
Camera permissions
Apps that have the permission to access your camera tin take screenshots of your activities, take photos and videos of you and your friends, and ship those images and video files back to the author of the app.
Similarly, if an app has access to your microphone, whatsoever recording tool on your phone can be manipulated to record y'all without your noesis.
Location permissions
The location feature on your telephone can tell burglars when you lot are abroad from your dwelling house and tin tell the owners of location-restricted websites and services that you are outside of their operating area and so they tin cake you.
Operating system and storage permissions
Giving an app permission to access your storage allows data thieves to steal your data. It also opens the door to ransomware that can encrypt all of the files on your device and make them inaccessible until you lot pay for the decryption primal.
Assuasive an app to gain control of system settings could mean you lose access to your phone.
Turn off location services completely
On Android, the merely way you can turn off admission permissions is on a per app basis, every bit described above. This is the case with all categories except for the Location services of your telephone. These can exist turned off completely.
Turning off location services defeats geo-restricted websites that try to cake your access from other countries. You lot can bypass their restrictions past using a VPN. Yet, many sites also check your location in the operating system and that defeats that masking activity of the VPN considering it gives away your real location.
The strategy of turning off location services completely doesn't always work to get you into overseas websites. For example, even if you have a VPN operating, the YouTube Television set site won't give yous access unless it can besides check your phone's location. You lot also lose the benefit of beingness able to runway your progress along a road in a web map service.
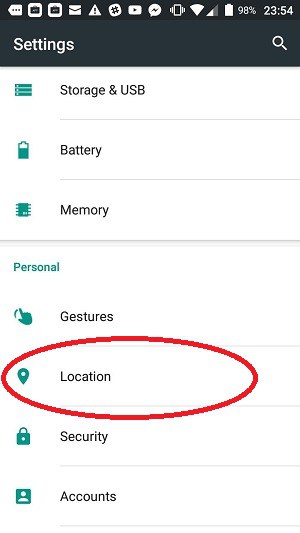
However, if you want to turn off the location services on your Android phone, go to the Settings screen, scroll downward to the Personal section, and tap on Location.
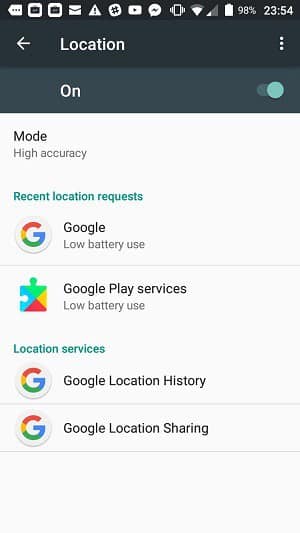
Click on the slider at the top of the Location screen.
Android permission problems
Loapi Trojan
An example of a malware nightmare that will ruin your phone if you let it to access the organization is the Loapi Trojan, which Kaspersky Labs spotted towards the end of 2017. This malware is advertised every bit an antivirus utility or an developed content app. One time information technology is installed, the app will constantly need permission to admission the organization. Information technology will repeat the demand over and again until you tap on Let. You restart your telephone to try to plow the app off, but that won't work. When your phone starts up again, the first thing yous will see is that demand for admission.
The Loapi Trojan has a wide range of malicious functions. These include:
- Launching DDoS attacks on command on other internet-connected devices
- Cryptocurrency mining
- Frantic web folio access to bump up income from recorded visits
The blueprint of the Trojan enables its controller to load upwardly new attacks on your telephone at will. So this is a backdoor that will allow a constant stream of attacks to download onto your phone.
When investigating this Trojan, Kaspersky Labs loaded it onto a smartphone. Inside two days, the excessive processing caused by the virus caused the device's battery to bloat and the phone's cover to warp. Basically, if you unintentionally download Loapi, yous might likewise throw your phone away.
The Trojan's antivirus sweep volition detect other antivirus programs running on your phone and alert you to allow removal of those programs, which Loapi falsely labels equally malware. Again, the app will non take Deny for an respond. The prompt to allow the removal of those programs will not stop until you tap on Permit.
If you have Loapi on your phone, you might try all of the steps outlined in this guide to remove its permissions. However, the defense force mechanisms of this malware suite will lock the phone and shut down the settings screens, making it impossible for you to revoke its admission rights. This vicious app is just one example of malware that will return your phone unusable.
Joker malware
A more recent case of problematic malware is Joker malware. This family unit of malicious apps has been attacking Android users since 2016. Media outlets reported in 2020 that the malware had infected many different apps. The malware returned in 2021, updated, targeting millions of Android users. Joker malware is at present so widespread that cybersecurity firm Zscaler has created a dedicated team to enquiry the threat.
Joker'southward apps are knockoffs of legitimate apps. When you download them from Play or a unlike market, the app contains no malicious lawmaking other than a 'dropper. After a delay of some hours or even days, the dropper and then downloads a malicious component and so drops it into the app. Apps recently constitute hiding Joker malware include:
- Gratuitous Affluent Bulletin
- PDF Photo Scanner
- delux Keyboard
- Comply QR Scanner
- PDF Converter Scanner
- Font Style Keyboard
- Translate Free
- Saying Bulletin
- Individual Bulletin
- Read Scanner
- Print Scanner
When y'all download an infected app, this tricks the Android notification organization by asking for permission to read all notifications. Once you grant this permission, it hides all notifications of malicious behavior. Since these notifications are subconscious, criminals tin:
- Steal personal information
- Access and copy your contact listing
- Monitor your text messages
- Sign you up for fraudulent services
- Send text messages to premium numbers
If you have downloaded any of the apps listed above, you should immediately uninstall them. To find and delete apps on Android, follow these steps:
- Open the Google Play Store app
- At the top right, tap the contour icon
- Tap Manage apps & devices so Installed
- Go through the list of displayed applications
- Next to the app yous want to remove, tap Uninstall
Wrapping Upward
It's time to take back control of your Android device. You demand to adjust all of those permissions and tighten up the security of your phone.
Be very conscientious about where you get your apps from. Never answer to spam SMS messages and avert following links in web pages while using your telephone. You also need to brand a vow to pay attention to those permission notifications and select Deny unless there is a very good reason to tap on Allow. If an app won't work without those permissions, you may want to consider uninstalling information technology.
Run across also:
Cybercrime stats
Identity theft stats
Ransomware stats
Source: https://www.comparitech.com/blog/vpn-privacy/secure-android-app-permissions/
Posted by: trubytendought.blogspot.com


0 Response to "Should Att Smart Wifi Have Draw Over Other Apps And Modifie System Permission On My Phone?"
Post a Comment